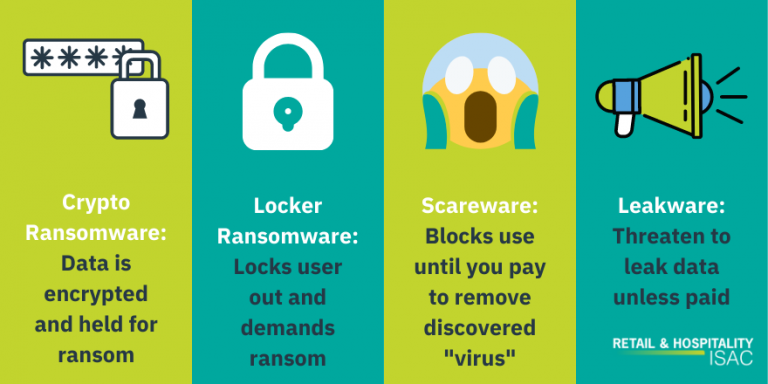
Crypto Ransomware
The first ransomware attack, known as the AIDS Trojan, hit the healthcare industry in 1989, but it’s only been in the last decade that strains such as CryptoLocker, Petya, NotPetya, WannaCry, TeslaCrypt, and Locky have pushed ransomware to the forefront of cybersecurity discussions. These strains have variations in the way they deploy, but the basic premise behind them is the same: encrypt the victim’s data and demand payment in exchange for its decryption. This is the most common type of ransomware attack and is known as crypto ransomware. It tends to be more common as there are large potential payouts for encrypting the data of large companies that have the resources to pay heavily for the return of sensitive information such as intellectual property and customer data.
Locker Ransomware
There are, however, other types of ransomware, which also demand payment but do not encrypt data. For example, locker ransomware simply locks the user out of their machine. The files are not usually targeted, but other computer functions are disabled, so the user only has the ability to interact with the ransom window. The naming here is a bit misleading because many of the well-known crypto ransomware strains, such as CryptoLocker, do encrypt data but have the word “locker” in them since they’re essentially locking the data by encrypting it. Actual locker ransomware is only targeting that one machine which is why it is much less high-profile than crypto ransomware which can spread throughout an extensive network. It is usually individuals, as opposed to companies that are targeted with locker ransomware, sometimes as a result of visiting a compromised site, such as pirating site. Since this ransomware is only attacking that one machine, it is also a lot easier to just not pay the ransom here. So threat actors employing this method will typically use social engineering, posing as an agency with authority to collect a fine or enact some type of punishment for wrongdoing that led to the infection.
Scareware
Another type of non-encrypting ransomware is scareware. Scareware poses as a virus detection software and will either lock your computer or simply flood it with pop-up windows rendering it effectively useless until a payment is made to remove the “virus” that the software has detected. Like locker ransomware, this is usually a smaller scale operation targeting individuals who have accessed compromised sites that infected their computer.
Leakware and Double Extortion
As a company, you’re likely to be dealing with a crypto ransomware attack, but increasingly in the last few years, threat actors are not relying solely on encryption anymore. If you’re the victim of an attack, you may also be subject to additional threats to publicly expose your data. A type of ransomware attack called doxware or leakware threatens to leak sensitive information if a ransom is not paid. Bad actors are using this method of double extortion to apply additional pressure to organizations that may have backups or other methods of retrieving their data besides paying the ransom.
Defending Against Types of Ransomware Attacks
RH-ISAC provides members with resources to defend against ransomware attacks. One of the most straightforward ways to protect against any of these kinds of attacks is following safe online practices and implementing policies for this at your organization. RH-ISAC provides security awareness training resources that educate employees about common scams such as phishing that can lead to malware infection. Members also have access to resources such as trend reports and daily intelligence briefings that identify common malware strains and TTPs peers are seeing so you can be aware of warning signs. Learn more about RH-ISAC membership.


